Adversary Personas is an improvisational role-playing game designed to help teams think broadly and creatively about their cybersecurity threats.
Developed by researchers at the University of California, Berkeley, the game focuses on the who of security, by forcing players to ask: who might our adversaries be, what do they want, and what would they be willing to go through to get it?
The game can be played by teams of employees in any organization. It is recommended for groups of between 2-10 people.
Get the game
How to play
Get a group of people together—preferably people who are working to protect the same resources (e.g. digital networks, company data, etc).
Step 1: What are you protecting?
Before starting the game, the group should work together to list out all the things they are protecting. Think broadly. Go beyond sensitive data, and list all that is valuable to your organization, such as clients and customers, the community you share in your work, the security or stability the work provides you and your loved ones. What else? List these on a sheet of paper.
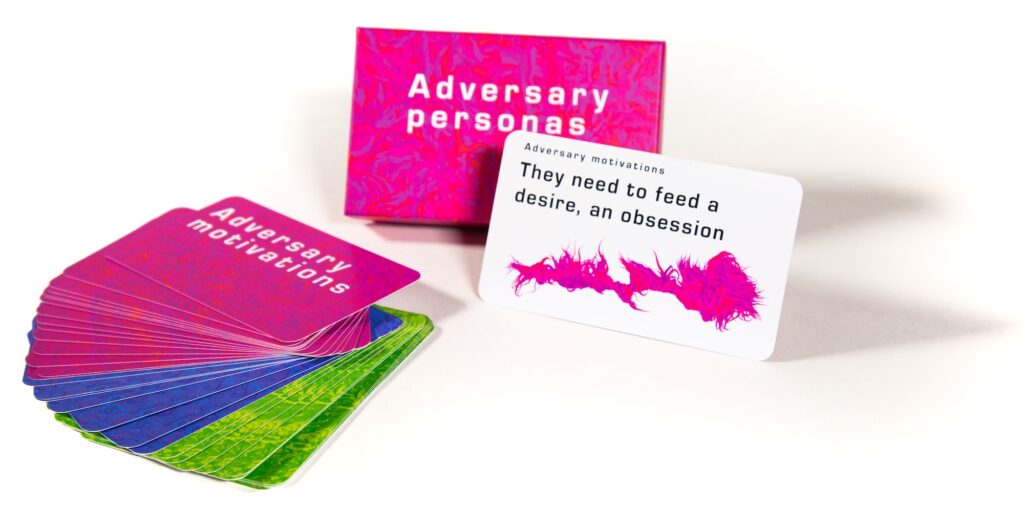
Optional: Pass around the Impacts cards. Have everyone look through them for inspiration.
Step 2. Who are your adversaries?
In the previous step, you listed some of the things you want to protect. But adversaries want things too. They have desires that conflict with yours. What do your adversaries want? What are they going to do to get it?
Pass around the Motivations deck. When you’ve got the deck, take the top card, and read it out loud in the first person. For example, “I need money.”
Flesh out this character a little more. For example, “I work for our company, and my rent is going up, and I need to find the extra money somewhere, or my kids and I are going to be priced out of town.”
Then, say what you are going to do about it. For example, “I need money, and I’m going to skim pennies off of every transaction that comes through our service.”
You have just described an adversary. Note down a memorable name for him/her. For example, the character described above might be called “the cash-strapped programmer.” This is an adversary persona.
Tip: Make this process interactive. Once the person with the card gets into character, the group can ask that person questions as if they’re the character. It’s a great way to get your adversary in the room. How often do you get to interview your attackers?
Step 3. What do adversaries have at their disposal?
Distribute all of the Resources cards around the group. Everyone should have a few Resources cards in their hand. With the cards you’re holding, survey the personas you’ve generated. Use them to highlight or challenge your assumptions. For example, were you assuming the lone hacker didn’t have money, or political power? What if they do?
In some cases, adding an unexpected resource may create a new personas. If they do, note them down and give them a new name.
Step 4. Who are you most concerned about?
Pick the top one to three personas you think are most likely for your organization. If you can, act out the attack as if you are that attacker! See if you can create a proof of concept that maps to that attackers’ needs or desires.
Frequently Asked Questions
Who should play adversary personas?
Adversary Personas is designed for any group of stakeholders—companies, public-sector organizations, non-profits, or other organizations—that need to protect themselves against digitally-mediated threats. The primary audiences for the game are UX designers, technology professionals, and managers who are responsible for cybersecurity training or engagement in their organizations.
Who created Adversary Personas?
Adversary Personas was created by Nick Merrill, a research fellow at the UC Berkeley Center for Long-Term Cybersecurity and recent Ph.D. graduate from the UC Berkeley School of Information. The game was inspired by Nick’s experience with theatrical improv, as well as by the design practice of user personas.
Does playing this game really improve cybersecurity awareness?
Our research is still ongoing, but our initial studies have found that people with no security training are able to identify security risks that even security specialists were not aware of. We will update this page with studies on the game as they pass through peer review.
I have a question about Adversary Personas. How can I contact you?
Contact Nick Merrill at ffff (at) berkeley (dot) edu
Acknowledgements
These cards are inspired by my experience with theatrical improv, by the UX practice of user personas, and by Denning et al’s Security Cards, by Hendry et al’s Envisioning Cards, and by Elsden et al’s Speculative Enactments. Visual design of the cards by Noura Howell. Thanks to Charles Weir for the printable version of these cards.