CLTC has launched the CLTC Bulletin, a new “publication” on Medium, the popular blogging platform. Designed to be a more informal outlet for our communications, the CLTC Bulletin features news, research and opinions from CLTC staff and researchers. Here are summaries of some of the stories you can already find at the CLTC Bulletin:
CLTC has launched the CLTC Bulletin, a new “publication” on Medium, the popular blogging platform. Designed to be a more informal outlet for our communications, the CLTC Bulletin features news, research and opinions from CLTC staff and researchers. Here are summaries of some of the stories you can already find at the CLTC Bulletin:
Don’t Call It A Hack
The Daylight Lab has been working to jettison the negative baggage tied to the word “hack” and reclaim its positive origin story. In a blog post on Medium, Daylight Lab director Nick Merrill argued that journalists should be more specific in their use of language, avoiding clichés like “hack” and using terms describing the specific nature of the cyberattack or breach. “Call it a crime, or an attack, or perhaps a digital assault, but don’t call it a hack,” Merrill wrote. “This simple language move will help to shift the conversation on cybersecurity and motivate more determined, informed, and collaborative action that will make the digital world a safer place.” Cybersecurity journalists Joseph Marks from The Washington Post and Dell Cameron with Gizmodo tweeted about the blog post, noting their own frustrations in finding words to describe attacks. Read the CLTC Bulletin post here.
Cybersecurity Imagery Dataset

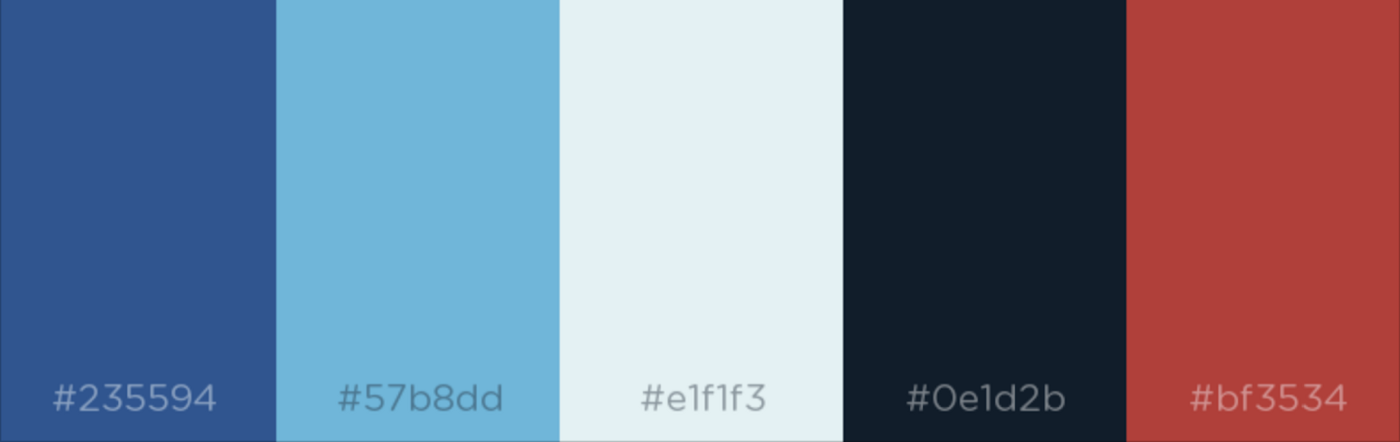
From hackers in hoodies to padlocks on laptops, the images used to represent cybersecurity often fail to capture the range of threats, bad actors, or human harms of cyberattacks. To better understand this issue, the Daylight Lab captured two years of Google Image Search results from 28 different cybersecurity-related search terms to analyze the current state of how security is represented on the web. Initial findings confirmed that blue and gray are the dominant colors of cybersecurity imagery. “Our dataset allows for the first large-scale analysis of security’s visual representations,” Merrill wrote in an article on the CLTC Bulletin. “By describing current trends and tendencies, we can highlight opportunities for new types of imagery, describing tropes to avoid — or to riff on in imaginative ways.” The project was mentioned in the “Quick Bytes” section of Politico’s Morning Cybersecurity newsletter, and Sean Lawson, a cybersecurity reporter, wrote about the project for Forbes. “The Daylight Lab’s dataset allows us…to analyze the images for other themes and patterns of interest,” Lawson wrote. “It creates a baseline of knowledge about the current state of cybersecurity imagery that can be used to help us do better.” Read the CLTC Bulletin post here.
Internet Fragmentation: Beyond ‘Free’ and ‘Closed’
Governments, firms, and citizens are debating to what extent the Internet is, or should be, a global infrastructure for communication and commerce. In these debates, the Internet is supposedly becoming increasingly fragmented, subject to “splintering” across national borders. A new project by the Daylight Lab aims to bring value-free measurement to this debate about Internet fragmentation. “Rather than building normative judgments into our metrics, we aim to measure the underlying architecture of the Internet,” Nick Merrill explained. “We seek to enable normative discussions about what values to maximize, and descriptive discussions about how best to navigate a (potentially) fragmented world.” The DSRL built a dataset to measure Internet fragmentation through proxy measures on four different layers of the Internet “stack,” and they were able to produce “profiles” of different countries’ Internets. Read more on the CLTC Bulletin.
The Future of Cybersecurity Education via Public Interest Clinics
On Wednesday, November 20, Citizen Clinic Deputy Director Steve Trush presented at the 2019 National Initiative for Cybersecurity Education (NICE) Conference in Phoenix, AZ. In his talk, Trush provided an overview of Citizen Clinic, the first public-interest cybersecurity clinic, which has a mission to support the digital safety of civil society organizations. He discussed how the clinic model is helping to broaden and diversify the cybersecurity workforce by delivering hands-on learning opportunities to students, whether they go on to work in the public sector, private industry, or non-profit organizations. “We want to see similar clinics at other universities and colleges,” Trush said. “To support this vision, we will be open-sourcing our curriculum, as well as sharing lessons we learn through 2020. We also want to explore how to better integrate clinic programs within community colleges or make them accessible to non-degree-seeking students.” Read more on the CLTC Bulletin.
Adversarial Machine Learning

Recent years have seen a rapid increase in the use of machine learning, through which computers can be programmed to identify patterns in information and make increasingly accurate predictions over time. While machine learning models have many potential benefits, they may be vulnerable to manipulation. Cybersecurity researchers refer to this risk as “adversarial machine learning,” as AI systems can be deceived (by attackers or “adversaries”) into making incorrect assessments. We created a short “explainer video” and brief report designed to provide an overview of adversarial machine learning for policymakers, business leaders, and other stakeholders who may be involved in the development of machine learning systems, but who may not be aware of the potential for these systems to be manipulated or corrupted. Read more on the CLTC Bulletin.