On Wednesday, March 6, the UC Berkeley Center for Long-Term Cybersecurity (CLTC) and CNA’s Institute for Public Research hosted a session at the 28th annual RSA Conference (RSAC), one of the world’s largest information technology security conferences, at the Moscone Center, in San Francisco.
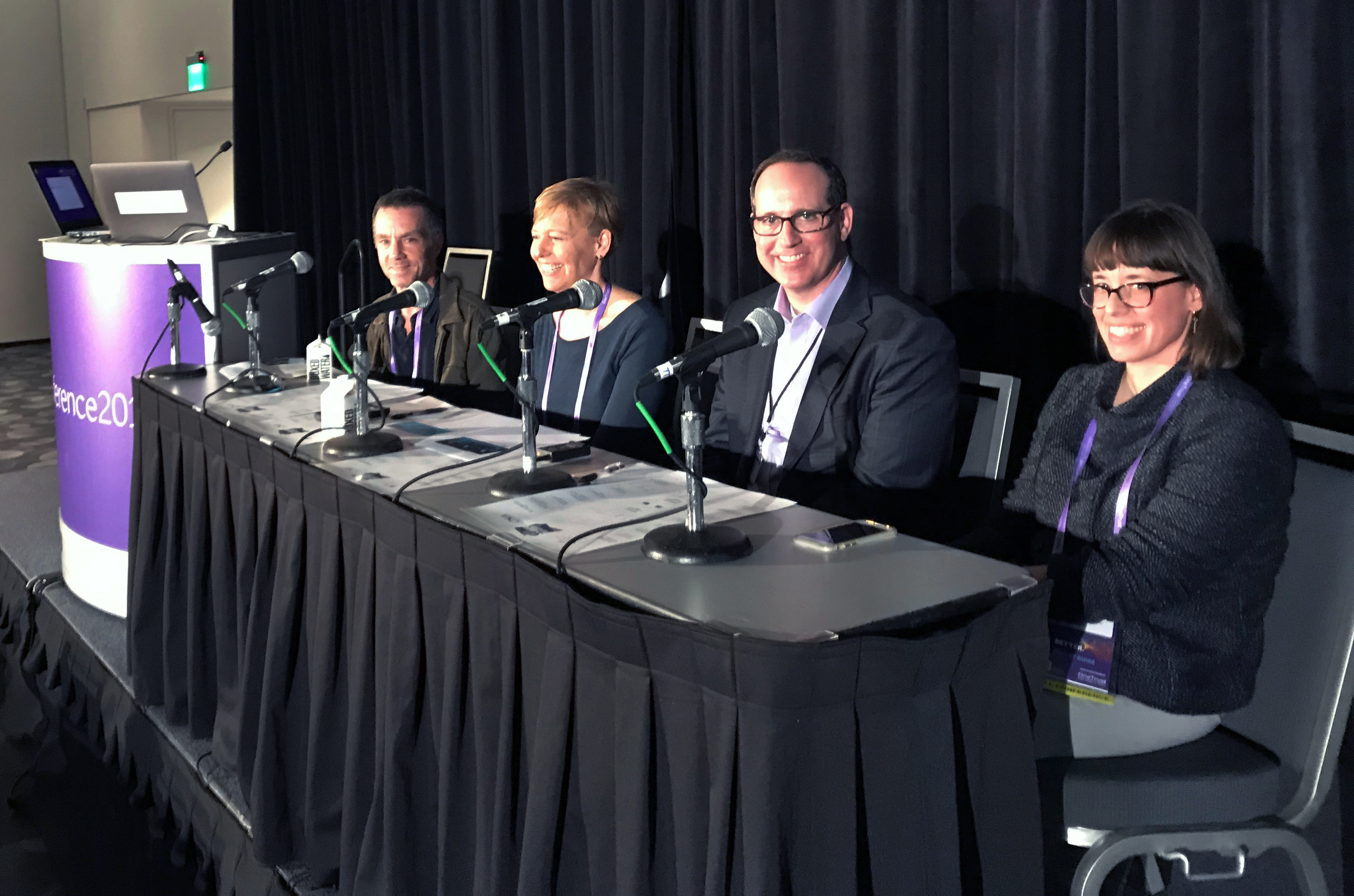
 The session, “Future of Cybersecurity Scenarios: Anticipating the Cybersecurity Challenges of the Future,” was facilitated by Steve Weber, CLTC’s Faculty Director, and Ann Cleaveland, Executive Director. Other facilitators included Dawn Thomas, Associate Director of Safety and Security at CNA’s Institute for Public Research, and Alan Cohn, Partner and Co-Chair of Blockchain and Cryptocurrency Practice at Steptoe & Johnson LLP.
The session, “Future of Cybersecurity Scenarios: Anticipating the Cybersecurity Challenges of the Future,” was facilitated by Steve Weber, CLTC’s Faculty Director, and Ann Cleaveland, Executive Director. Other facilitators included Dawn Thomas, Associate Director of Safety and Security at CNA’s Institute for Public Research, and Alan Cohn, Partner and Co-Chair of Blockchain and Cryptocurrency Practice at Steptoe & Johnson LLP.
In an introduction to the session, Steve Weber explained that cybersecurity is no longer a specialized set of issues that only cyber professionals need to worry about. “Cybersecurity, broadly defined, is the master problem of the Internet era that affects everyone in industry, government, academia, and civil society,” he said. “The problem is evolving much faster than our ability to understand it, and different countries and societies will grapple with these challenges in different ways. If we can gain foresight into those differences now, it will better situate us to tilt the digital world in a direction that is more secure and beneficial to people and societies.”
 More than 150 RSAC attendees participated in the session, which introduced Cybersecurity Futures 2025, an international initiative that aims to shape a forward-looking research and policy agenda around cybersecurity that is intellectually and practically robust—and broadly applicable across countries and regions. The session presented a truncated, 50-minute version of an eight-hour workshop that CLTC, CNA, and the World Economic Forum’s Global Centre for Cybersecurity have held in seven locations across the globe. The goal is to help decision-makers in government, industry, and civil society reduce frictions, seize opportunities for cooperation, and better prepare for the future.
More than 150 RSAC attendees participated in the session, which introduced Cybersecurity Futures 2025, an international initiative that aims to shape a forward-looking research and policy agenda around cybersecurity that is intellectually and practically robust—and broadly applicable across countries and regions. The session presented a truncated, 50-minute version of an eight-hour workshop that CLTC, CNA, and the World Economic Forum’s Global Centre for Cybersecurity have held in seven locations across the globe. The goal is to help decision-makers in government, industry, and civil society reduce frictions, seize opportunities for cooperation, and better prepare for the future.
The conversation centered around three scenario videos that told logical stories about how forces of change could overlap and combine to create a cybersecurity landscape in 2025 that is meaningfully different from what we see today. Session participants were seated at round tables and asked to discuss as a group each scenario’s ideal outcome, and to consider the issues that would keep them up at night.
 In a blog post for RSAC, Tony Kontzer wrote about his experience at the session. “With all of these thoughts about future security and privacy crises swirling in our heads, we were then asked to fill out March Madness-style brackets pitting outcomes against each other, with good outcomes on one side, and bad outcomes on the other, voting via the RSA Conference app, and sharing real-time results.” The outcome attendees felt was most positive was a future in which societies make significant progress against complex problems such as health care, climate change, and poverty, using immense data sets and the capabilities to process them. Two negative outcomes ran neck-in-neck on the other side of the bracket: one in which society fails to understand how humans process information in the cyber age, and in which we cannot recognize manipulation or become more resilient to it; and a second in which data manipulation becomes even more difficult to detect, leading institutions that rely on trust to collapse. The results made clear the security professionals in the session believe the future is all about big data.
In a blog post for RSAC, Tony Kontzer wrote about his experience at the session. “With all of these thoughts about future security and privacy crises swirling in our heads, we were then asked to fill out March Madness-style brackets pitting outcomes against each other, with good outcomes on one side, and bad outcomes on the other, voting via the RSA Conference app, and sharing real-time results.” The outcome attendees felt was most positive was a future in which societies make significant progress against complex problems such as health care, climate change, and poverty, using immense data sets and the capabilities to process them. Two negative outcomes ran neck-in-neck on the other side of the bracket: one in which society fails to understand how humans process information in the cyber age, and in which we cannot recognize manipulation or become more resilient to it; and a second in which data manipulation becomes even more difficult to detect, leading institutions that rely on trust to collapse. The results made clear the security professionals in the session believe the future is all about big data.
Cohn led a brief discussion about the results by posing a couple of open questions to the audience, asking how they might address the negative outcomes or foster an environment to realize the positive outcome. Ultimately, the group emphasized education, transparency, and trust as tactics that will foster an environment for the most positive byproduct as well as address the most worrisome byproduct.
Next, Weber shared some of the preliminary findings and insights that took shape from the results of the international workshops. These insights are discussed in further detail in “Cybersecurity Futures 2025: Insights and Findings,” a report that offers three overarching observations (below) and proposes five new landscape elements to reframe the decision-making environment:
- “The finding that is most relevant for security professionals here at RSA is a deep sense that the digital technology we work with is becoming more firmly linked to the goals of national power,” Weber said. As recently as three years ago, a “free and open internet” narrative that placed governments squarely in the background of the digital environment was still robust. That ideology, which in some respects was naive, appears to be largely gone. “Data nationalism” of some kind is now a given.
- There is a strong sense of disillusionment with vague notions of “cybernorms” or expectations about how people and companies will behave and manage that transition. Workshop participants around the world were hard-pressed to attach
concrete meaning to norms, or to articulate how discussions about norms would lead—as opposed to follow—emergent behaviors. - Keeping a hold of the upside, there is a sense around the world that, in turning the conversation to the security side of the issues, we are at risk of losing sight of the magnificent positive potential that is possible with these digital technologies if properly managed and secured.
To conclude the session, CNA’s Thomas invited attendees to go to the project website and to continue to interact with Cybersecurity Futures 2025 following the conference. Thomas also challenged the audience to hold their own futures session with their organizations’ leadership over the next few months. “By strategically engaging with the scenarios and sharing the insights with your colleagues,” she said, “you’ll provide the project with more data so that we can better understand and set priorities to address these issues.”